Three MuckRock users filed FOIA requests from 2013 to 2015 for FBI files on The Tor Project, Inc., the developer of Tor. The software enables (in theory) untraceable access to both the regular internet and a network of websites inaccessible through other browsers, commonly called the “dark web.” Each request returned radically different sets of records, most predating the first request, and all linked only by their lack of substantial information.
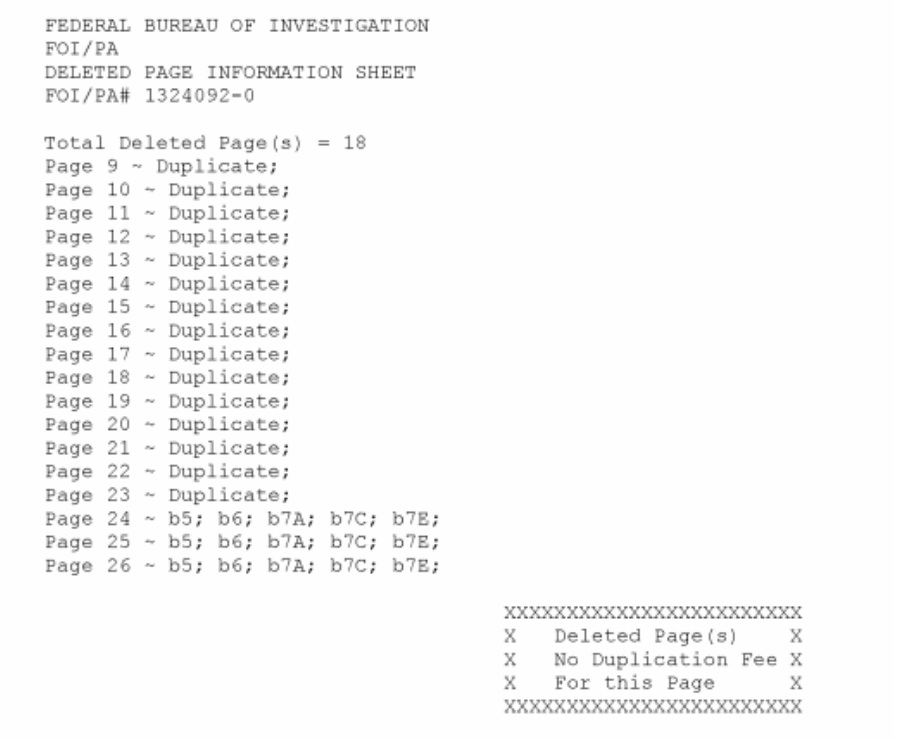
Two, more targeted, requests about the online black market Silk Road and the digital currency Bitcoin also yielded documents referencing Tor, none of which were included in the broader requests.
Tor - with a user base ranging from political dissidents and the those wary of ad tracking to major drug traffickers and spies - was partially developed and largely funded by the U.S. government for use by the intelligence community.
Former Tor developer Runa Sandvik’s request for all records referring to The Tor Project received solely the portion of the FBI’s Domestic Investigations and Operations Guide outlining investigative methods, which makes no unredacted reference to Tor or the dark web. The release suggests a confirmation that Tor plays a noteworthy role in the FBI’s surveillance process, whether as a tool or an obstacle to be overcome.
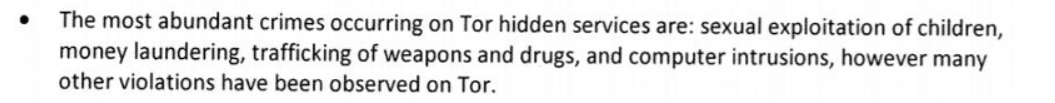
Child pornography and fears over extremist uses of secure and faceless currency exchange are the two main focuses of the few documents the Bureau has gradually released, with a glaring absence of more than fleeting mention of Silk Road.
In files respondent to requests about the anything-goes marketplace, which the FBI shut down for the first time months before fulfilling one of the requests, Silk Road is named only as an example of the uses of Bitcoin or as a segue into a child pornography report.
One 2008 investigation by the Innocent Images Task Force into a website hosting child pornography seems to have ended after agents on the case started getting 404 errors. Dark web sites dedicated to criminal activity are known for frequently changing their URLs to avoid legal troubles.
Several years later in 2012 the FBI’s Operation Torpedo, likely named after the unfortunate wordplay of the older website, resulted in numerous arrests and the closure of many child pornography sites. The relatively high-profile operation goes entirely unmentioned in each set of files.
Last Thursday, Europol and the U.S. Department of Justice announced the seizure of two of the dark web’s largest criminal marketplaces in a multi-agency operation led in part by the FBI.
We’ve filed again. In the meantime, read the FBI’s Domestic Investigations and Operations Guide released to Runa below.
Image via Pexels