In 2014 MuckRock user Scott Ainslie received an unexpected response from the Department of Homeland Security. Despite requesting DHS files related to a series of foreign cyberattacks codenamed “Operation Aurora,” they responded with a video clip and 840 pages of documents relating to a different Operation Aurora that DHS conducted in 2007.
Run by the DHS Control Systems Security Program, that operation was focused on hacking into a 27-ton generator — 4,000 pounds heavier than an M3 Bradley tank — and opening its circuit breakers long enough for the machine to slip out of sync. This caused the generator to experience “tremendous over-torque stresses,” and do what happened in the video below:
Blow up.
This test, which lasted all of three minutes, took almost a full year to plan, was all done to prove the existence of a cybersecurity flaw called the “Aurora Vulnerability.” This vulnerability deals with what are called digital protective relays which manage circuit breakers in generators, motors and other parts of power grid substations. All of America’s infrastructure relies on these protective relays to make sure the machines that run our country don’t go out of sync.
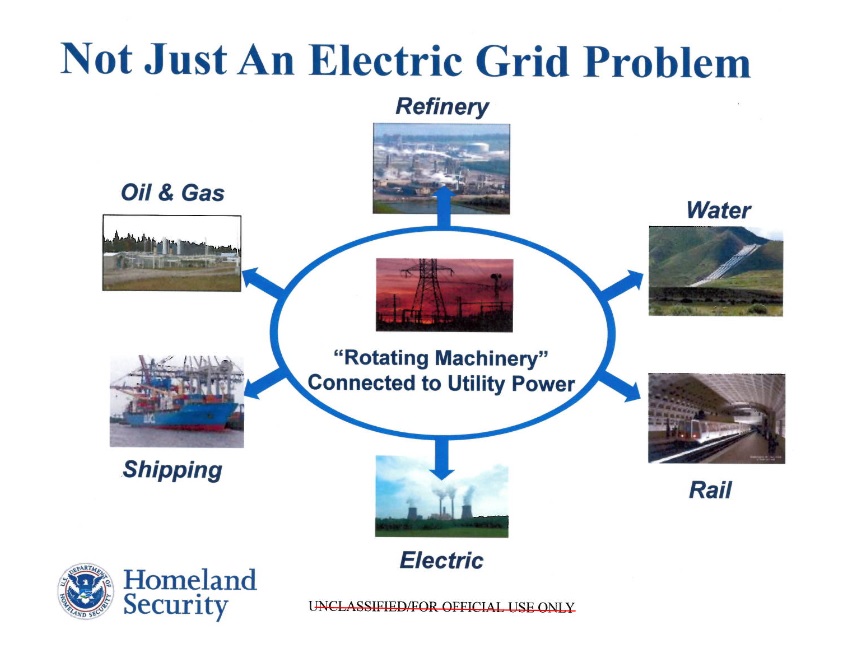
What this project proved is that hackers could override our infrastructure’s defense mechanisms and turn it against us, affecting facilities like oil refineries, water plants, and chemical factories.
And that the US government is on the case, blowing up generators and spending over two million dollars on a single project trying to figure out how to solve this potentially catastrophic design flaw. Which is why the response - or lack thereof - to the project is so confounding.
Read the full report embedded below, or on the Operation Aurora FOIA page:




