9283 Tags
surveillance
7 Projects
Street Level Surveillance: Biometrics FOIA Campaign
The Spy In Your Pocket
CVE Watch
Cell Site Simulator Census
Police Surveillance Tech in Mississippi
114 Articles
Whistleblower complaint leads to plans for widespread DNA surveillance of immigrants
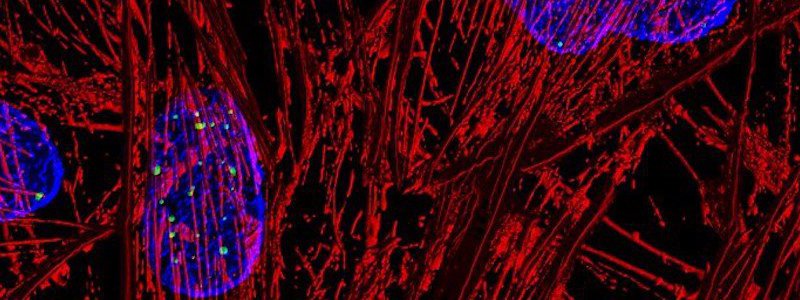
Last spring, the Department of Homeland Security started collecting DNA at United States borders for the first time. Since then, DHS has quietly begun to implement the largest expansion of government DNA collection and storing of biometric information in more than a decade.

Controversial Obama-era counterrorism program continues uninterrupted in Colorado
New documents raise questions about Denver Police Department continued participation in a controversial Obama-era counterrorism program.

What’s the smart city future like in Wisconsin?
Sitting on the shores of Lake Michigan, Racine, Wisconsin lays claim to inventing the hairdryer and garbage disposal. With Milwaukee to its north and Chicago to its south, the town is tapping into that legacy as the first municipality with fewer than 100,000 residents to be chosen for the Smart Cities Readiness Challenge.

MuckRock readers want to know: What drone use is going on in your area?
MuckRock announced that it would be looking at the extent of drone use by municipalities, counties, and states throughout the country. Since then, individuals from Connecticut to California have responded to the call.

Does your local government use drones? Help us find out
Five years ago, MuckRock teamed up with Motherboard to conduct a massive survey of drone use by local police departments. We want to update that effort, and we need your help to do it.
136 Requests
Completed
Freddy Martinez sent this request to the Chicago Police Department of Chicago, IL
Completed
Freddy Martinez sent this request to the Chicago Police Department of Chicago, IL
Completed
Candice Garcia sent this request to the Chicago Police Department of Chicago, IL
Completed
Candice Garcia sent this request to the Chicago Police Department of Chicago, IL
Completed
Freddy Martinez sent this request to the Chicago Police Department of Chicago, IL
1 Question
| Better information |