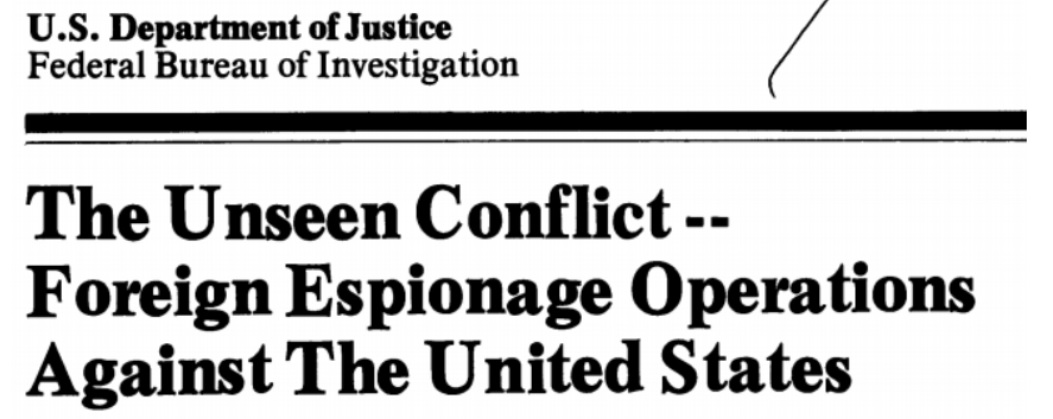
A pamphlet written by the FBI’s Intelligence Division in 1983 and signed by then-FBI Director William Webster addressed “the unseen conflict” of Soviet espionage operations against the United States. The pamphlet argued, quite reasonably, that the only way the Bureau could defend against threats like these was if people who were approached by Russian agents remembered that “the FBI is as close as your nearest telephone.”
The memo offers several tips and pieces of advice, beginning with not underestimating the KGB’s capabilities, or to expect them to operate as they did in television and movies. When contacted, those with and seeking security clearances were expected to report the encounter to their Security Officer. If the foreign operatives began attempting to cultivate a personal relationship or rapport with the subject, it should be seen as a red flag due to it being a “key first step” in recruitment. Casual meetings also needed to be avoided, as did offers of gifts, favors, or support - especially those that seemed to come without strings attached.
Even if the meetings turned out to be innocent, the pamphlet stressed that it was critical to contact the FBI or a Security Officer immediately if a situation aroused one’s suspicions - no matter the circumstances. The Bureau and the appropriate Security Officer could help, but “this assistance cannot be rendered if the employee remains silent. Of course, it is much better for an employee to reveal a suspect relationship voluntarily, rather than have it come to light in the course of an investigation.”
To stress the point further, the pamphlet warned quite clearly that a citizen’s failure to act responsibly in regards to such foreign contacts could render other security efforts moot.
The pamphlet also lists several motives and techniques Russian and other Soviet operatives would use in their attempts to recruit someone: greed, blackmail, national pride, exploitation of emotions, “false flags”, ideology, naivete, and revenge. Each of these motives was illustrated with at least one example. Greed, for instance, was perhaps the most common and the most effective approach, as well as being the easiest to mask due to its veneer of legitimacy. In these scenarios, a “businessman” would turn out to be “a professional intelligence officer using their business association as a “cover” for clandestine intelligence collection.”
The second example, blackmail, often involved compromising Americans overseas “through sex and other ploys,” often recording the Americans or otherwise finding a way to exploit the encounter. Since this type of blackmail works much more effectively when the subject remains a secret, victims were encouraged to report it as soon as they became aware of what was going on. According to anecdotes, the half-joking KGB response was similar with agents, asking for a copy of the tape to show their wife.
Appeals to national pride were typically “aimed at emigrants” from Eastern European and Soviet Bloc countries.
The exploitation of emotional involvement was fairly straightforward, using a real or manufactured relationship as leverage to force or encourage compliance.
The “false flag” approach would see the target approached from someone claiming to be associated with an American ally or other group which the individual would want to help.
Ideological beliefs were also particularly exploited, though the focus had changed over the years. In the ’50s and ’60s, ideological approaches largely focused on those with “communist sympathies.” A more modern approach would be based on someone’s other views, such as a “desire for international harmony and world peace” or nuclear disarmament. Other ideological beliefs, such as a deep seated opposition to CIA or views on NATO, could similarly be used.
According to the pamphlet, foreign intelligence service would also exploit an American’s naivete. Using this approach, a foreign intelligence officer would rely on an American simply not seeing anything wrong with what they were doing. This might be based on principles of business, freedom of speech, the sharing of scientific advancements, or even negotiations based in politics and economics.
The final motive explored by the pamphlet was a desire for revenge, a self-explanatory and relatively easy to manipulate motive. It was, after all, “a quick way to wreak vengeance” while profiting off the bargain. “Needless to say, if an intelligence officer divines that a targeted American is dissatisfied … the spy will zero in on this discontent.”
The solution to all of this, however, remained simple - avoid these meetings to begin with, and if they occur report them immediately to a security officer or to the FBI. The worst thing that someone could do would be to try to handle it on their own. The Bureau warned that “any attempts by untrained or uninformed persons to handle hostile efforts on their own could result not only in personal disaster, but may also interfere with the FBI’s counterintelligence effort.” Nor was there any need for someone to go it alone - for anyone in the United States, “the FBI is as close as your nearest telephone.”
Although the specifics and the context have changed over time, all of the techniques described above remain viable and popular. Several recent high profile examples demonstrate this, such as the use of Russian “businessmen” who worked to recruit Carter Page. Other examples, of course, can be remarkably difficult to prove - such as when they are exploiting someone’s preexisting ideology. Philip Agee, for instance, is known to have worked with foreign intelligence services - but there is no public evidence that they approached him based on his ideology and dissatisfaction with CIA, but rather that he approached them based on it.
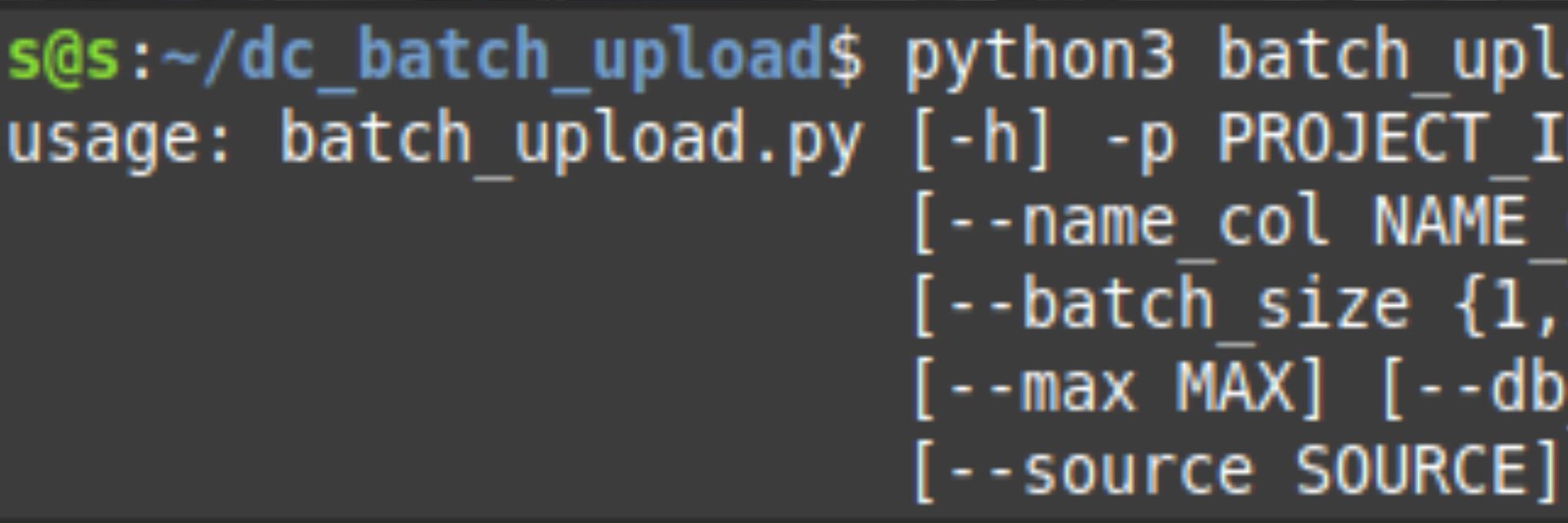
You can read the full pamphlet below or click here to file a new FOIA request or MDR to get the FBI or CIA to release more information.
Like Emma Best’s work? Support her on Patreon.
Image via U.S. Air Forces Central Command